Digital substation security
The rapid pace of change in the electric power grid creates a challenging environment for asset owners and operators of an electricity infrastructure to monitor the activities of industry and standards organizations, develop an understanding of the security impacts of new technologies, and assess and monitor cyber security risks.

Power system operators in a utility require not only comprehensive backgrounds in the physical monitoring of field devices, but also cyber monitoring of intelligent electronic devices (IEDs) in a digitalized substation.
Thus, a comprehensive approach is required to utilize cyber–physical system (CPS) interactions, to provide insight by various monitoring tools, architectures, guidelines, and testing results.
To address the need for improved operations and visibility in the power grid infrastructure, companies in the utility industry have begun to adopt information and communication technologies, such as TCP/IP and Ethernet.
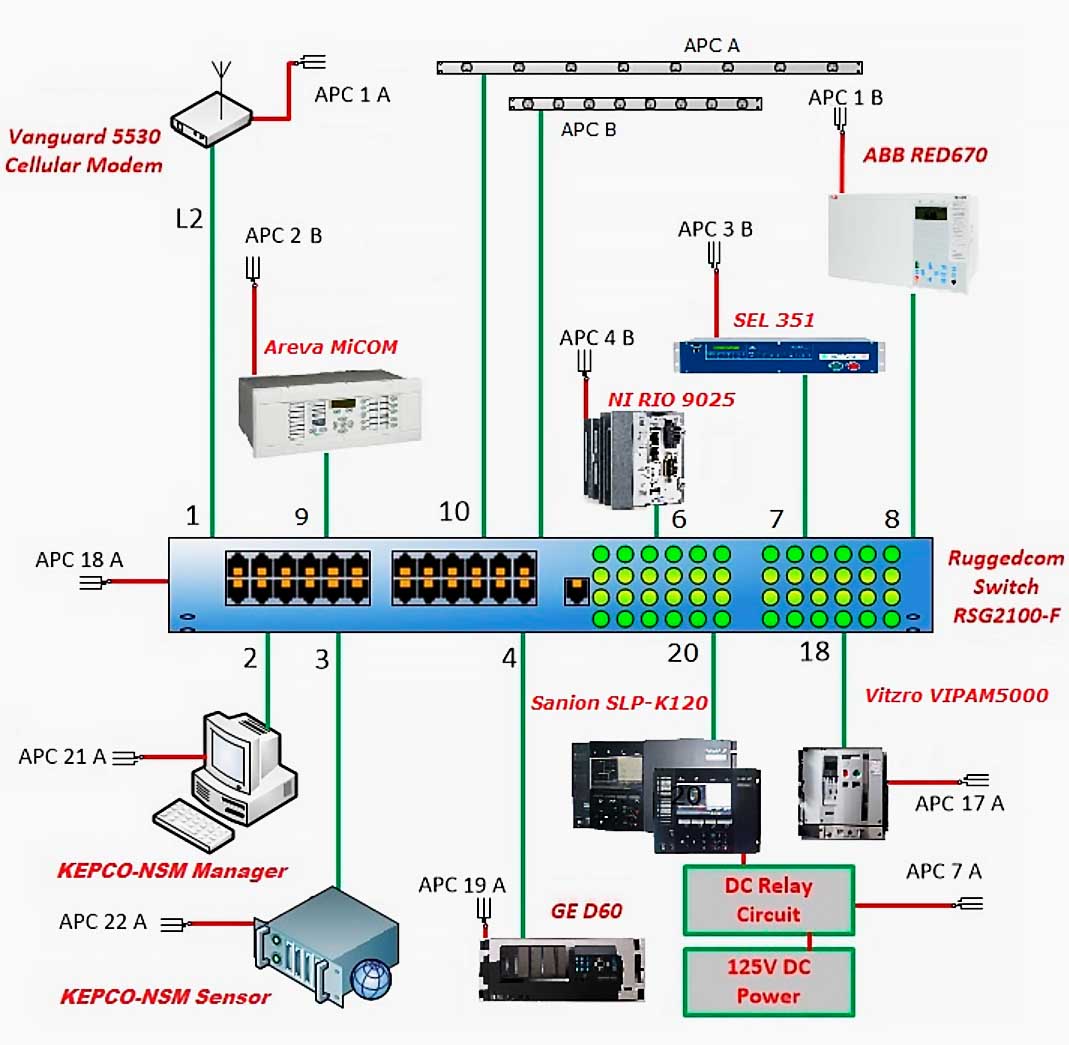
With this adoption, IT-centric network and system management (NSM) tools are widely used to monitor and manage communications with and between intermediate cyber systems and field devices.
International Electrotechnical Commission (IEC) 62351-7 represents a technical specification that attempts to address the need for a single set of NSM definitions regarding the security for the IEC 61850 protocol.
Previous literature (“Power Systems Management and Associated Information Exchange—Data and Communications Security—Part 7” and “Network and System Management: Advanced Application of the IEC 62351-7 Standard and Utility Pilot Project”) has provided a transformation of IEC 62351-7, so that it can be implemented.
Chen et al. propose a modeling of cyber security status of the digital substation by the Markov decision process (MDP), but it only focuses on the design of the detection of cyber security attacks in a limited-use case.
Moreover, the model does not consider cyber–physical analysis concerning IEC 62351-7-based network and system management.
| Title: | Behavior Analysis and Anomaly Detection for a Digital Substation on Cyber-Physical System – YooJin Kwon, SangYoum Lee, Ralph King, Jong In Lim and Huy Kang Kim |
| Format: | |
| Size: | PDF 8.90 MB; XLSX 124 KB |
| Pages: | 24 |
| Download: | Right here | Video Courses | Membership | Download Updates |
| Spreadsheets: | Right here |


Very good articles
How reactive power can be monitored in digital sub station.
EEp isvery nice